Cyber Security is the protection of digital data, computer systems, computer networks, and other technological devices and information from digital attacks and damages. This is done with the help of various technical processes and practices that are specially developed to protect the digital aspects of a device. This attack on digital assets is known as a cyber attack and the person who initiates is known as a cybercriminal or a hacker in popular terms.
Types of Cyber Security
Cyber security is now an important part of every individual because of the fast-paced digitalization of almost everything around us, especially the digitalization of finances. There are various cases of cyber fraud every day wherein hackers steal money from victims using hacking or they steal their sensitive confidential data in exchange for money.
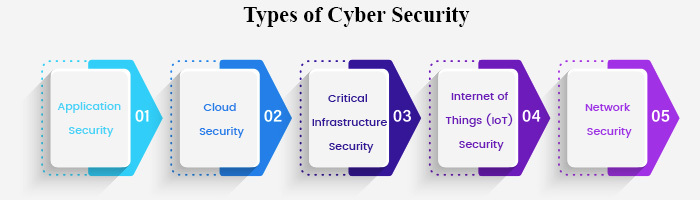
There are several ways in which a hacker can hack your device or system and hence there are several ways in which cyber security professionals can protect you. There are different types of cyber security domains to deal with different security threats. Each domain focuses on solving a particular problem or cyber threat. Read: Top 10 Cyber Security Colleges In India!
Following are some of the most common and preferred types of Cyber Security domains that are extremely efficient and loved by most organisations.
#1 Application Security
Any computer system or digital device has various applications in them. Many of these applications require the personal or any confidential data of the user. For instance, social media applications require the personal information of the users while online money transaction applications require the bank details of the user. Such information is highly sensitive and can cause great damage to the user if gotten into the hands of malicious cybercriminals.
Therefore, application security is built to protect the applications that are operating on the device or in the cloud from getting hacked. The application security is built at the time of designing the application. Security engineers have to consider user authentication, user privacy, how the data is going to be handled, etc.
During the designing, developing, and implementation of an application or software, insecure processes might happen resulting in vulnerabilities that the hackers are eagerly looking for. Application security addresses these vulnerabilities and protects the application and the entire device or system from cyber attacks.
#2 Cloud Security
Just like an actual cloud stores water droplets in it, a digital cloud stores data, networks, applications, and servers in it. This cloud is hence virtual storage present in the omnipotent internet, and whatever is stored within can be accessed through the Internet.
The Internet is something that everybody is using in current times. People with advanced knowledge of the internet can hence take advantage of the ones who are not so tech-savvy. This sometimes results in cyberattacks on vulnerable users who hold little technological knowledge. Since the internet is open to all, cloud security becomes extremely essential without which the data stored on the cloud will be easily accessible to third parties.
Hence, Cloud security comes into play. It is used to protect and secure the data and applications of any user that are stored on the Cloud. Protecting cloud data includes everything, from when the data is stagnant (just stored) in the cloud, to when the data is in use and to when the data is in motion, which means when the data is traveling to and from different clouds or within the same cloud. Cloud security helps consumers to ensure not just customer privacy but also regulatory compliance standards.
#3 Critical Infrastructure Security
Just like the name, Critical Infrastructure Security is responsible to secure and protect systems, networks, and any other digital assets that are of national as well as international importance. Be it national safety, national and international economics, or public health and safety.
There are many organisations and companies in every country that fall under the category that needs Critical Infrastructure Security- ranging from financial services, energy, and natural resources, Defence sector, transportation, communications, medical sector, food and agriculture, and a few more. Most of these organisations are government organisations like the Banks, factories under the Ministry of Defence, PSUs related to Communications, Transport, and Energy.
Because of the increasing digitalisation, almost all of the data of these organisations have become digital which makes it more vulnerable and exposed to cyber threats. Hence, the security of this data has become a great concern. Critical Infrastructure Security is what protects this data from hackers. Highly specialised cyber security professionals are hired by such organisations as it is not at all an easy task.
#4 Internet of Things (IoT) Security
Before understanding the Internet of Things (IoT) Security, let us first understand what actually is IoT. You must have definitely heard of Alexa and how it is able to connect and control other appliances and devices like television, refrigerators, speakers, lights, fans, air-cons, etc. This is what an IoT is. It is a network of more than one device connected together that are capable of collecting and exchanging data within this network. For example, if your mobile phone is connected to the Alexa, then the data on your phone is accessible by the Alexa as well depending upon the privacy policies.
IoT Security is responsible to develop robust privacy policies and network security systems to protect the data from getting leaked or from the network getting hacked. There are grievous consequences if even a single device from the network gets hacked as data can be accessed in real-time because of the embedded software and sensors.
Given below are examples of some IoT devices used in various sectors and industries for you to understand the importance of IoT Security.
- IoT devices used in Businesses- smart security cameras, door locks, trackers for vehicles or other goods, sensors on industrial machinery to capture data, and alike. If there is a breach in the security of these devices, it can put the company infrastructure in grave danger.
- IoT devices used by Consumers- smartphones, smart home appliances, smartwatches, door locks, house security systems, semi-automatic cars, and alike. A breach in the security of these IoT devices might lead to the leaking of personal information and data from your smartphones, robbery in houses, stalking, and even car accidents.
- IoT devices used by Government- traffic monitoring devices, tracking devices used by police or intelligence agencies, and devices used in natural disaster alerts. You can imagine the chaos that can be caused if hackers manipulate traffic light signals. However, the motive of such attacks is usually money. Any attack that is done in order to extort money is known as ransomware. We will discuss this in detail in the types of cyber threats section.
#5 Network Security
The corporate network is often described as the heart and soul of an organisation. This is where almost 90% of the company’s data is stored. The security of this network is the topmost priority of the cyber security team of any organisation. Network security is responsible for detecting and resolving security loopholes that affect the network architecture as well as Operating Systems (OS).
Network security is not just about using software, it is rather a strategic combination of both software and hardware designed to secure sensitive data stored within the data centre of the corporation. Hardware in network security might include servers, devices, or other appliances that perform some security functions. An example for network security software is an anti-virus system.
Security breach in a corporate network has the capability to destroy the entire organisation as the hackers can gain access to information as crucial as the financial statements, login credentials, passwords, and more. Hackers mostly try to get into the network framework of a company as it houses the kind of information that criminals are seeking. This makes network security a very vital type of cyber security.
Now that we know the major types of Cyber Security, let us also know the cyber threats against which these security types are used.
Types of Cyber Security Threats
Cyber Security Threats are cyber attacks like illegally hacking a device or setting up viruses in a device to steal, damage, or delete data with evil intent. The motive of such attacks is usually money or revenge. Depending upon the type of device or the intention of the attack, or the receiver of the attack, there are multiple types of cyber threats.
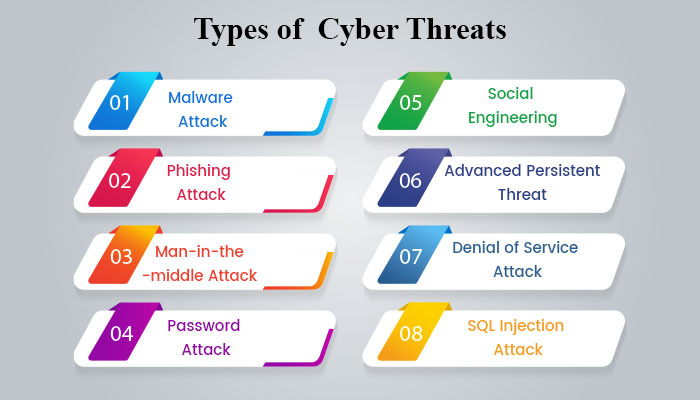
#1 Malware Attack
Malware is short for malicious software. Malware is the most common type of cyber threat and can be carried out in multiple ways. This type of cyber attack is usually in the form of a link or an attachment that is sent to the user disguised as though it has been sent by a legitimate source. As soon as the user clicks on that link, the malware gets installed on the device and damages the OS for its malicious purpose. In short, malware gives unauthorised access of your device to a third party without you knowing.
Malware cyber attacks can be anyone or a combination of two or more of the following types.
- Virus
Virus is the most common type of malware that when installed on a device spreads quickly throughout the operating system and corrupts the data of the device. A virus within a single file can spread and damage all the others in the system.
- Ransomware
Ransomware is the kind of malware that when installed on a device encrypts important files and data and locks them down. Hackers then ask for ransom in exchange for the data of the user.
- Spyware
Spyware is the type of malware that gets installed on the device without the user knowing. The device works just fine so the user is unaware but the spyware secretly records the user’s actions on the device. With this, the hacker can get access to details such as login passwords and even credit/debit card details.
- Trojans
Trojans are malware that is disguised as authentic software. The users are tricked into setting up these trojans in their system. The rest is very simple, the hacker easily gets access to the user’s system and can do whatever they wish, way before the user realises the attack.
- Adware
Adware is short for Advertising software. These are just advertisements and pop-ups that you see on various websites.
Adware is not a threat unless they bring in other malware with them.
This means that adware itself is not a threat but it might contain a virus or other type of malware that can slow down your system or corrupt files or hack your browser.
- Botnets
A botnet is a network of various malware-affected systems/devices used to perform digital tasks on the internet without the user knowing. An example of a botnet is the various comments you must have seen on social media platforms like Youtube and Instagram. These comments are either spreading hatred through tons of malicious comments or to popularise something or someone.
#2 Phishing Attack
Phishing attack in simple terms is a cyber-attack in which cyber attackers fool users by disguising themselves as legitimate sources. For instance, they might send a fraudulent email that appears to be coming from an authentic source. This email contains links or attachments which install malware into the user’s device.
#3 Man-in-the-middle Attack
In this type of attack, the hacker somehow takes over the user’s IP address to install the malware on the user’s device. It usually happens during transactions between two parties. Once the hacker gets control over the IP address, it becomes easy to secretly intercept the communication line between the user and the second party. Now, the data can be easily stolen and tampered with. This usually happens because of unsecured Wi-Fi networks.
This type of cyber attack usually happens during online transactions. For example, you bought something from an online shopping site, then when you checkout and make payment, the hacker gets access to the information path between you and the shopping site’s server. When this happens, the hacker can easily know your login credentials, passwords, and even your credit/debit card or other bank details.
#4 Password Attack
This is one of the most common and easiest types of cyber attack. However, this attack is not very useful against highly secured devices, systems, and networks. This is because this attack is nothing but the hacker cracking the user’s password by using codes to try all the possible alphanumeric combinations. Therefore, you must have noticed that almost all the websites ask you to set unique passwords by using special characters.
#5 Social Engineering
This is the type of attack which is not completely digital. This means that first actual people obtain personal information about people usually from social media platforms. The hackers then communicate with these people disguised as legitimate people/businesses. They trick and manipulate users to reveal confidential information like OTPs (One Time Password) with the help of which, these hackers can steal data (usually money).
All the above types of cyber threats are the ones that are usually carried out against individuals or small organisations and companies. To target big corporations and organisations, hackers use advanced techniques to hack into the servers of these big companies as they are highly secured. Since the target is big, the losses are even bigger. Ransomware is one of such threats.
The other most common ones are described below:
1. Advanced Persistent Threat (APT)
In an Advanced Persistent Threat (APT), hackers get into the network of the organization’s server and access it for a prolonged period. In this period of time, they secretly continue to gain confidential and sensitive information about the organization. This information can include an important code of the product of a tech company or the financial deals and details of a company or the personal information of the company’s clients.
2. Denial of Service Attack
In the Denial of Service Attack, the network of an organisation is deliberately flooded with traffic of pseudo requests. This is done to leave the actual legitimate service requests unattended. This leaves the system with vulnerabilities and loopholes for hackers to seep in.
A type of this threat is the Distributed Denial of Service (DDoS) attack. In a DDoS attack, multiple systems are used to release the attack. This makes the network disabled for a while and the hackers use this time to install other malware. You could say that a DDoS is kind of a Botnet with the capacity to infect millions of systems at once.
3. SQL Injection Attack
SQL Injection attacks happen with database-driven websites. In this type of attack, the cybercriminal manipulates or tampers a standard SQL query in the database of the company to hack their system. The hacker does this by inserting (or injecting) some codes into the company’s server to obtain important information from the database to be able to manipulate it.
The hacker then gains the access to edit or delete tables and view confidential data. The cybercrime industry has seen a boost in recent years as there are fewer professionals to tackle it. Hence, the demand for cyber security professionals has increased incredibly.
A career in cyber security is considered one of the best in the country currently. There are many high-paying cyber security jobs but for only highly skilled professionals as cyber security is more about practical skills than theoretical knowledge. However, this does not mean that you do not need formal education in cyber security to get good jobs. To gain practical experience as well as academic knowledge of the subject, you can pursue online courses on cyber security. Read: Cyber Security Salary India!
This is advantageous as you can use the time that you save because of the online mode in practising what you learn. You will have ample time to practice as you can even pursue part-time jobs or internships to learn about the subject more closely to gain exposure and hone your skills. You can also pursue short-term certificate courses side by side. To learn more about cyber security online courses, you can visit College Vidya and get all the details.

















